Digital Shockwave: How the Handala Breach Exposed Israeli–Emirati Secrets and Unleashed a Devastating Cyber Strike on the UAE

A sophisticated cyber operation attributed to the Iranian-linked hacking group known as Handala has sent shockwaves through regional security and intelligence circles, revealing the extent to which digital warfare is now reshaping the balance of power in the Middle East. According to well-confirmed information, the group successfully penetrated the personal phone of former Israeli Chief of Staff Herzi Halevi after a prolonged and highly complex infiltration that spanned several years. The operation culminated in access to an extensive archive of highly sensitive material, estimated at approximately nineteen thousand files.
The scale and nature of the breach indicate a level of planning and persistence that goes far beyond opportunistic hacking. This was not a single-point intrusion, but rather a long-term intelligence operation designed to map, monitor, and ultimately exploit a high-value target. The files reportedly extracted include strategic military maps, internal documentation of classified meetings, and detailed personal data, all of which collectively provide a rare window into decision-making processes at the highest levels of Israeli security leadership.
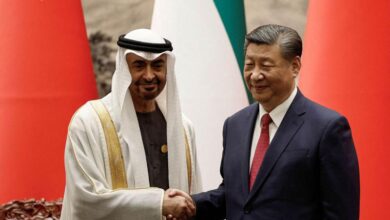
What makes this breach particularly significant is the content linking Israeli officials to undisclosed engagements with Emirati counterparts. According to the leaked material, some of the most sensitive documents detail secret meetings held in so-called crisis rooms, involving high-profile Emirati officials. These revelations suggest a deeper and more operational level of coordination between Israel and the UAE than previously acknowledged in public discourse.
The group has further indicated that its archive extends beyond written documents to include recordings and photographic evidence of Israeli officials conducting undisclosed visits to the UAE. Samples released on the group’s online platforms are presented as proof of access, reinforcing the credibility of the operation and amplifying its psychological impact. Even limited disclosure of such material can introduce uncertainty and distrust within political and security networks.
The operation did not stop at intelligence gathering. In what was described as a punitive escalation, Handala launched a large-scale cyberattack targeting key institutions within the UAE. This phase of the campaign resulted in the destruction of vast quantities of data, with approximately six petabytes erased from critical systems. In addition, around one hundred and forty nine terabytes of highly sensitive information were extracted from the core infrastructure of three major entities in Dubai.
The magnitude of these figures underscores the severity of the attack. Data at this scale represents not only operational records but also institutional memory, financial transactions, security logs, and strategic planning frameworks. Its loss or compromise can disrupt continuity, weaken institutional resilience, and create long-term vulnerabilities that extend far beyond the immediate aftermath of the breach.
The motivations behind the attack, as articulated by the group, are framed in explicitly political and ideological terms. The operation was described as a response to what is viewed as a betrayal by UAE leadership, linking the cyber campaign to broader regional dynamics. This framing highlights how cyber operations are increasingly intertwined with geopolitical messaging and psychological warfare.
From an analytical perspective, the implications of this incident are multi-layered. At the strategic level, it demonstrates the growing capability of cyber actors to conduct sustained espionage against high-profile targets. The ability to infiltrate a device belonging to a figure of Halevi’s stature reflects significant technical expertise and access to advanced resources.
At the operational level, the breach raises serious questions about security protocols and the protection of sensitive communications. In an era where personal devices often serve as gateways to broader networks, their compromise can have cascading effects, exposing not only individual data but entire systems of coordination.
The exposure of Israeli–Emirati coordination adds another critical dimension. Such revelations can influence regional perceptions and alter the dynamics of existing alliances. They introduce a layer of uncertainty that complicates diplomatic engagement and affects internal calculations within both countries.
The cyberattack on the UAE further illustrates the shift toward using digital tools as instruments of deterrence and retaliation. By targeting data rather than physical infrastructure, the operation achieves a dual objective: inflicting tangible damage while maintaining a degree of deniability. This aligns with broader trends in cyber conflict, where the boundaries between espionage, sabotage, and strategic signaling are increasingly blurred.
The psychological impact of such operations is equally significant. The knowledge that sensitive information has been accessed, copied, and potentially distributed creates a persistent sense of vulnerability. It can slow decision-making processes, disrupt communication, and force institutions to divert resources toward damage control.
Looking ahead, this incident is likely to have lasting consequences for how regional actors approach cybersecurity. It underscores the need for stronger protective measures, continuous monitoring, and the development of more resilient systems capable of withstanding prolonged infiltration attempts. It also highlights the importance of integrating cyber defense into broader strategic planning.
In conclusion, the Handala operation represents more than a single breach. It reflects a transformation in the nature of conflict, where information itself becomes both the target and the weapon. The exposure of sensitive Israeli–Emirati interactions, combined with the scale of the cyberattack on UAE institutions, signals a new phase in regional confrontation, where the battlefield extends deep into the digital domain.
As the full scope of the breach continues to unfold, its impact will likely extend beyond immediate technical damage, shaping political narratives, influencing strategic alignments, and redefining the rules of engagement in cyberspace.